Both individually and collectively, the entire global population has become increasingly dependent on a constellation of satellites orbiting the Earth.
Developed for the military beginning in the 1970s, global positioning system technology has become ubiquitous, critical to banking, communications and navigation systems worldwide since the 1990s. Most people are familiar with the navigation properties provided by our smart phones, but GPS signals also serve as the prevailing global clock used by the systems that drive our tech economy.
DETAIL
The term black hat refers to hacking that violates computer security for personal gain or malicious intent. In contrast to exploitative hackers, a white hat hacker uses similar techniques protectively to discover vulnerabilities in cyber systems to help identify protective measures needed to secure these systems.
In fact, GPS technology is but one facet of cyber physical systems (CPSs) controlled or monitored by computer-based algorithms and integrated with the internet and its users. However, along with this connectivity comes a number of security risks and vulnerabilities.
CPS security is an inherently interdisciplinary domain. Most organizations offering security services focus solely on information technology or have expertise in only one aspect of cybersecurity, such as hardware, software or communications. Southwest Research Institute takes a holistic approach to cybersecurity and has staff with experience in all relevant areas. We specialize in “white hat” techniques to evaluate networks, systems, software and embedded devices.
About the authors
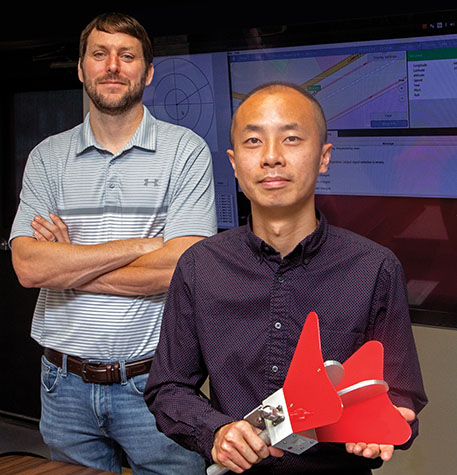
Vic Murray (left) is a manager in the Intelligent Systems Division leading automotive cybersecurity initiatives. He is a Certified Information System Security Professional (CISSP®). Dr. Jimmy Li is a research engineer specializing in antenna design, satellite communications and wireless communications for embedded systems.
GPS spoofing
SwRI has been developing automated vehicles for over 10 years, and we currently have 30 vehicles in our unmanned systems research fleet. We develop low-cost, high-performance perception, localization, path planning and control technologies for intelligent vehicles ranging from golf carts to SUVs to Class 8 tractor trailers. Automated driving uses a number of different localization technologies including GPS and vision- and LIDAR-based solutions as part of their localization and navigation packages.
Sensors, including GPS, are vulnerable to external interference, from both natural conditions and malicious actors. For example, GPS is often blocked, distorted or reflected by buildings, tunnels, overpasses or other structures. On the other hand, an attacker can block GPS data or transmit inaccurate coordinates using inexpensive, readily available radio devices.
The various industries dependent on GPS must evaluate the vulnerability of GPS receivers and their systems’ responses to interference in natural environments. However, because U.S. federal law prohibits over-the-air retransmission of GPS signals without appropriate authority, addressing this problem has been challenging. Fortunately, SwRI has recently developed a “legal” technique to spoof a GPS signal to understand the effects, particularly for automated vehicles that use GPS for positioning, navigation and timing.

Altered GPS

Normal
Velocity manipulation experiments with GPS signals caused vehicles to turn early or late, leaving the roadway.
So what is allowed? In general, the Federal Communications Commission (FCC) only allows entities to reradiate GPS signals inside a fully enclosed Faraday cage, under either an experimental license or a waiver, greatly limiting research and testing.
DETAIL
A Faraday cage is a mesh enclosure of conductive materials used to block electromagnetic fields.
In response, SwRI has developed and demonstrated a mobile GPS spoofing system that allows legal, real-world evaluations of GPS vulnerabilities. The two-component system includes a box placed on top of the vehicle’s GPS antenna and a separate ground station that controls the attacks remotely.
The system receives the actual GPS signal from an on-vehicle antenna, processes it, inserts a spoofed signal and broadcasts it to the vehicle’s GPS receiver. This gives the spoofing system full control over the vehicle’s GPS receiver and allows for real-time manipulation while a receiver is in motion. The operator can modify the signal in real time through a remote graphical user interface.
Attack modes
The system offers a full range of attacks to the GPS systems that thoroughly evaluate vulnerabilities to automated vehicles. These attack scenarios include modifying signal speed and timing as well as offsetting the location data or jamming.
A speed attack intentionally changes the speed associated with GPS signals, which can have various results. When implemented during a turn, the vehicle could turn too far and run off the road. When implemented before a turn, the vehicle could turn early or late, again potentially leaving the roadway. On straightaways, the effects are less apparent because the vehicle relies on another sensor for controlling speed.

SwRI has been integrating sensor technology with algorithms to develop automated vehicles for over 10 years. We have 30 different vehicles, ranging from tractor trailers to golf carts, in our research and development fleet. Now we are addressing cyber security for these intelligent vehicles.

Critical to creating a legal technique for evaluating vehicle responses to spoofed GPS signals is a shielded communications box to interface with a vehicle’s GPS antenna.
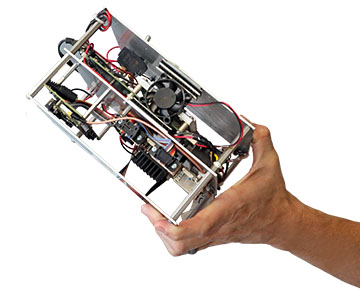
SwRI engineers developed a frequency translation system to receive, scramble and deliver modified GPS signals to automated vehicles for evaluation purposes. Legally evaluating the response to spoofed GPS signals in a moving vehicle in a natural environment was not previously possible.
When GPS signal speed is slowly brought to a halt, as the speed is reduced, the vehicle continues to drive at the same rate. Then, when the GPS location signal halts, the vehicle’s control system becomes unstable due to a lack of accurate positional feedback.
DETAIL
The 915MHz radio frequency, or ISM band, is reserved internationally for industrial, scientific and medical (ISM) purposes.
Timing attacks involve having the actual vehicle position relayed to the GPS receiver but delayed by several seconds, causing the vehicle to steer randomly due to a lack of current positional feedback.
Inserting an offset into a GPS signal can manipulate the perceived location of the vehicle. During our experiments, we offset vehicle location up to about 10 meters at a time in various directions. The vehicle under test immediately compensates and moves in the opposite direction, forcing lane changes, causing it to turn early or late or making the vehicle drive off the roadway.
Frequency translation
Most of the SwRI project used a Wi-Fi link to remotely control the spoofing system. The team also demonstrated over-the-air broadcast of the analog GPS signal using frequency translation to shift the base band to a frequency dedicated to industrial, scientific and medical purposes. On the receiver side, the signal was reconverted to the original base band using a similar setup and then sent to the GPS receiver.
Exposing vulnerabilities
As the vital role GPS plays in many modern-day systems continues to grow, exposing any inherent vulnerabilities of GPS is critical. Because U.S. federal law prohibits over-the-air spoofing, testing these vulnerabilities outside of an enclosed laboratory environment is problematic. SwRI has demonstrated the ability to legally transmit a spoofed GPS signal to a moving automated vehicle to analyze the system responses. We have demonstrated the technique in a relevant environment and are ready to help clients identify vulnerabilities and spoof-proof their technology.
Questions about this article? Contact Victor Murray or call +1 210 522 6589.

