Background
Controller Area Network (CAN) is the dominant network architecture used to connect electronic control units (ECUs) across virtually all makes and models of vehicles today. CAN is a broadcast messaging protocol where messages transmitted from one node are received by all network nodes. However, CAN was designed for reliability rather than security. This lack of security-focused design means that any one of these nodes can transmit a message to any other node and the receiver cannot verify the sender or that the message is unaltered.
Approach
The objective of this research was to determine the viability and performance of detecting various malicious attacks on an automotive CAN bus system. The specific malicious attacks that were investigated in this research includes: packet fuzzing/manipulation, denial-of-service, and diagnostic service exploitation. The research team created a system that allows for monitoring, analysis, and change of flow of CAN traffic. This setup can send and receive previously recorded CAN data packets between hardware devices via command-line utilities. The devices that were used includes a Raspberry Pi, CAN-to-USB interface, and a Linux computer to receive/monitor CAN data. Once the hardware setup was in place, the team wrote a Python-based application for the Linux computer that analyzes incoming CAN data through detection algorithms. The research team can then run an attack data set against the detection algorithms which compare the data to these previously calculated values from training. Any anomalies that may be present are then flagged.
Accomplishments
The team was successful at creating a system that uses automated data analytics to detect packet manipulation and denial-of-service-type CAN bus attacks. This research project has allowed SwRI to stay on the path to making advancements and expanding our skills in automotive security. The success the research team had with this project helped to differentiate the SwRI team in this field. Due to the success of this project, SwRI was not only able to expand the testing capabilities we offer our clients but also was able to elevate our standing as a rising member of the automotive cybersecurity field.
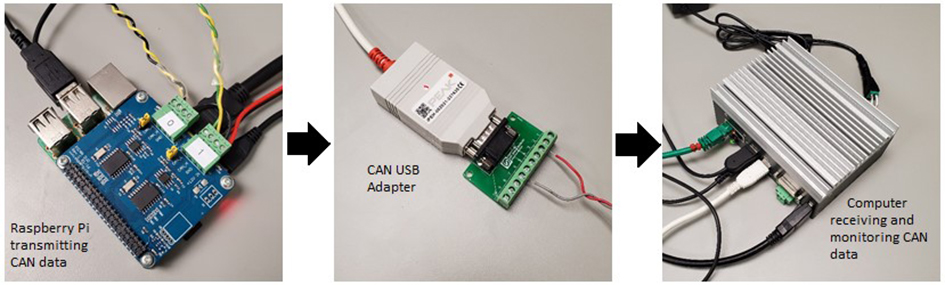
Figure 1: Hardware Setup.
