Background
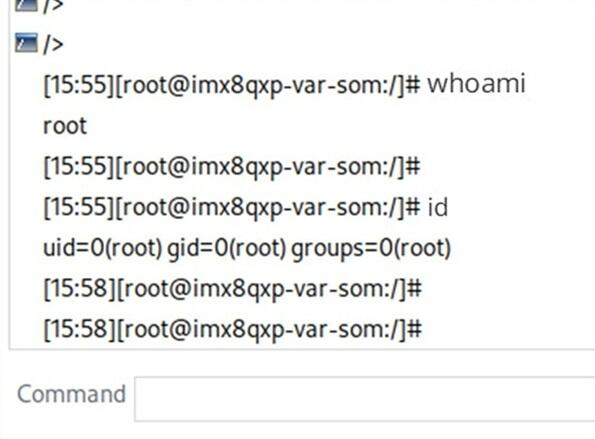
Figure 1: This image shows the outputs of the Unix "whoami" and "id" commands, confirming that researchers have full control of the RCU.
Remote Control Units (RCU) are environmentally hardened operational technology (OT) systems used at transportation terminals and critical facilities including manufacturing plants, ports, airports, rail terminals, power grids, water treatment facilities, and oil & gas infrastructure. RCUs are commonly deployed with a proximity card reader and used to authorize facility entry. However, because RCUs must be located outside the security perimeter, they present a potential attack surface for the facility network. As fully-functional computers located in physically accessible areas, RCUs are susceptible to cyber threats, making them a critical attack vector for facility networks.
Approach
The research team examined two versions of a popular model of RCU. This analysis included the security of communications leaving the RCU, and of the file structure on the system itself. Because physical access was a driving concern for this research, the team also assessed the possibility of exploiting inter-component communications (e.g., the connection from the proximity card reader to the single board computer).
Accomplishments
The analysis produced multiple security findings. Because these systems are used in critical infrastructure facilities around the country, SwRI disclosed this finding to both the manufacturer and to the Cybersecurity and Infrastructure Security Agency (CISA). CISA is currently drafting a Common Vulnerability Exposure (CVE) statement for publication.
