Background
The expansion of electric vehicles (EVs) and EV supply equipment (EVSE) drives advancements in battery technology. A critical component of battery pack technology is the battery management system (BMS), which ensures the EV’s functional safety by monitoring, protecting, and controlling the battery’s operations. These systems traditionally use wired communication, but the automakers are moving towards wireless communication to simplify design and reduce costs. This shift introduces potential cybersecurity risks associated with wireless communication. This presents an opportunity for SwRI to address cybersecurity issues and support the wider adoption of wBMS technology in the automotive industry.
Approach
This research project focused on evaluating the security of a wireless Battery Management System (wBMS) by conducting penetration testing. The approach involved system analysis, threat modeling, setting up testing environment, and executing attacks such as eavesdropping, spoofing, jamming, and machine-in-the-middle (MitM) attacks.
Accomplishments
When the peripheral and central devices are set up without any security, complete control of communication is possible. However, with security enabled, only partial control of communication is achieved.
During a jamming attack, BLE devices experiences interference that disrupts their communication channels, leading to higher packet loss and unstable connections. The peripheral device waits for data packets from the central device for a predetermined period before assuming the connection is lost and disconnects. Regardless of the security level, the communication stops and devices disconnect. Once the peripheral device unpairs from the central device, it sends out advertisement packets for connection.
The success of the jamming attack creates an opportunity for a MitM attack. In this scenario, an adversary device is set up to mimic both the central and peripheral devices. The adversary device establishes a connection with the genuine peripheral, allowing partial control over communication. The adversary device then imitates the peripheral to connect to the real central device, achieving complete control over communication. However, when security is enabled, the adversary device can only connect to the peripheral, resulting in only partial control of the communication.
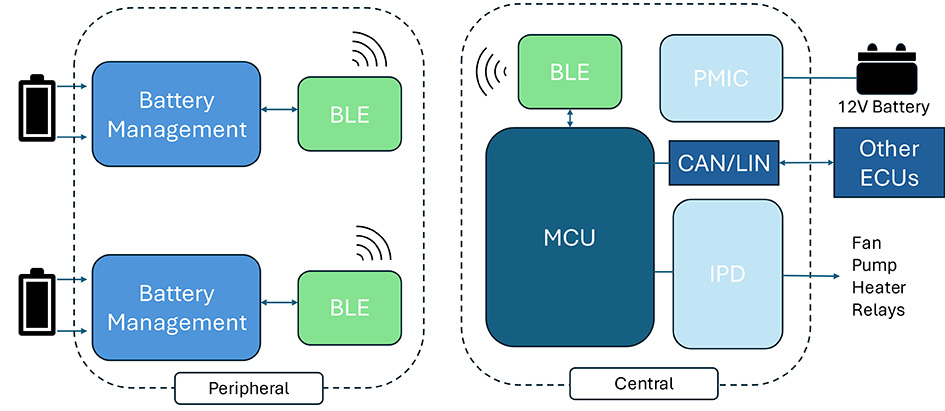
Figure 1: Test Bed architecture.
Resulting Project Work
10-29008
