Background
The FAA and multiple U.S. executive orders have emphasized the need to strengthening cybersecurity across critical infrastructure sectors. Executive Order 14028 specifically mandates the implementation of Zero Trust Architecture (ZTA) where suitable. As space infrastructure is vital to national security, economic activities, and global communication, improving its cybersecurity as directed by these executive orders will ensure it remains functional and secure.
ZTA is a security framework aimed at mitigating internal and external threats. While ZTA principles are well-established in terrestrial systems, their implementation in space systems encounter challenges with limited computational resources, bandwidth, and intermittent connectivity. This presents an opportunity for SwRI to develop a framework that meets space industry needs in meeting cyber requirements on Zero Trust.
Approach
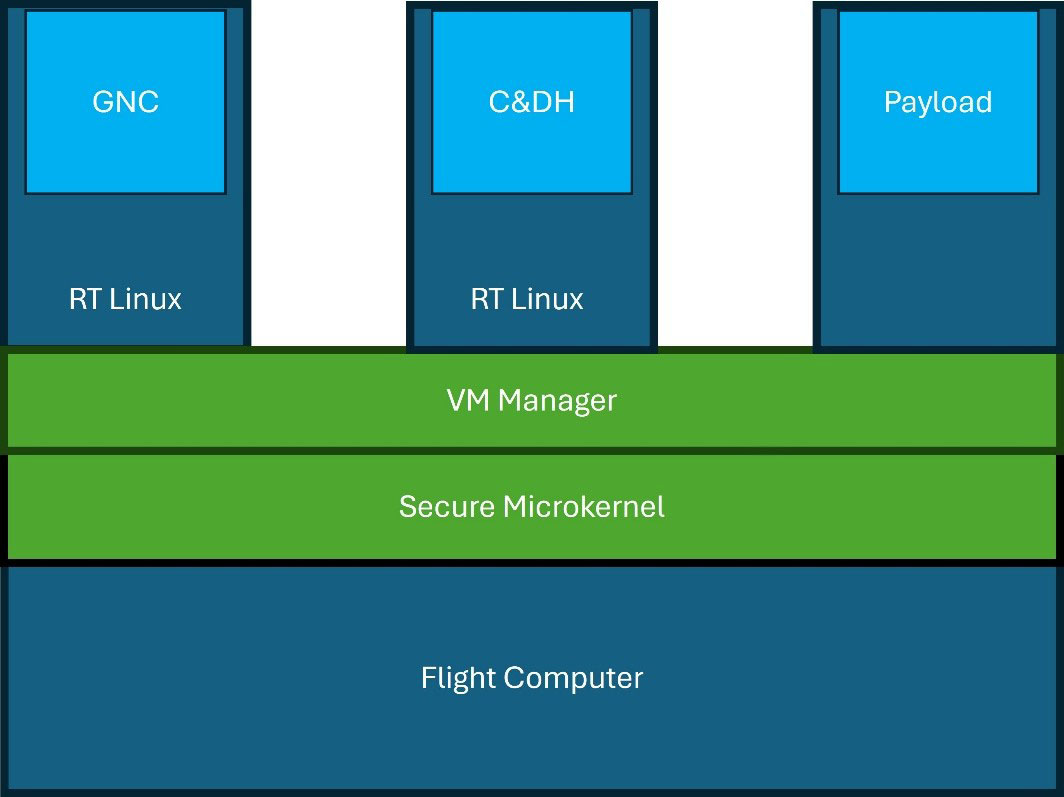
Figure 1: Software Architecture.
The objective of this research is to apply Zero Trust Architecture (ZTA) principles to the problem of cyber hardening flight software systems. The specific goals are detailed below:
Create an authentication and authorization framework tailored for flight software to authenticate every message, user, and device.
Implement least privilege access control to minimize the attack surface by granting users and devices only the minimum level of access necessary.
Apply micro-segmentation strategies by dividing the system into smaller, isolated segments to prevent lateral movement.
Explore the performance impact of implementing these features on resource-constrained hardware.
The ZTA leverages the seL4 Microkit framework as the foundation for Real-Time Linux images running core-Flight Software (cFS). Microkit is an operating system framework on top of the seL4 microkernel. It provides a set of abstractions that ease the design and implementation of seL4, leveraging the kernel’s benefits of security and performance. seL4 is renowned for being the world's first operating system kernel that has been formally verified, which means its correctness has been mathematically proven. This formal verification guarantees that the microkernel behaves exactly as intended, eliminating many security vulnerabilities typically found in traditional microkernels.
To accurately represent an aerospace environment, developers used the cFS framework to create a reference flight software system. The system was then micro-segmented based on data flows, and these micro-segmented images are run within a secure hypervisor setup in Microkit.
A comprehensive test was then conducted to benchmark the performance impact and verify the security features of the new system. This assessment aims to identify any potential bottlenecks or vulnerabilities. By thoroughly analyzing the system's efficiency and security measures, we can determine if the system can be effectively implemented in a real-world scenario.
Accomplishments
A reference flight software system is created using the cFS framework, incorporating a satellite software stack with separate data flows for Guidance, Navigation, and Controls (GNC), Command and Data Handling (C&DH), and payload operations. Performance metrics show reduced CPU usage when running cFS in Microkit. Latency is minimum impacted because timing synchronization between cFS applications has a greater effect than the hypervisor. However, virtualization increases RAM and thread usage because each Real Time (RT) Linux image requires its own vCPU and memory space. In contrast, a monolithic kernel allows all CPU cores to be shared across all data flows. This tradeoff may be valuable for systems with data flows of mixed criticality that don’t require all systems cores for each data flow.
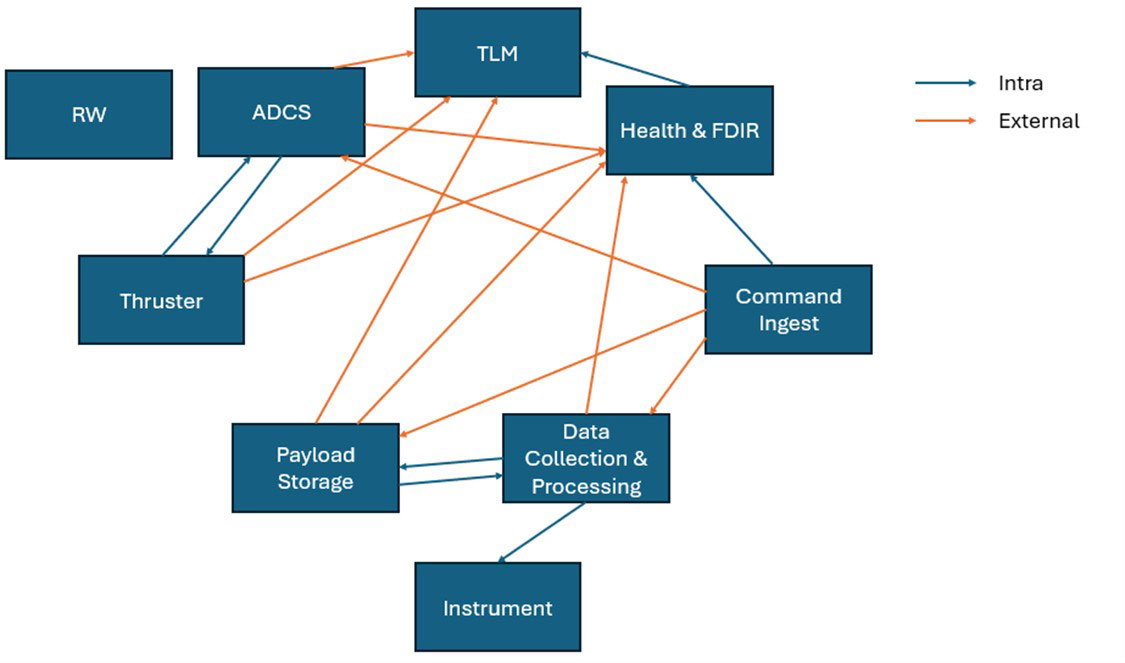
Figure 2: Dataflows between cFS apps.
