Background
5G is expected to contribute over $210 billion to North America’s GDP and comprise over 90% of all cellular connections by 2030 (excluding cellular IoT). This increased reliance on 5G communications highlights the importance of understanding the associated security risks. Previous generation cellular networks have shown that vulnerabilities in cellular communications can lead to severe consequences, including exposure of personal location, 2FA hijacking, and data exfiltration. SwRI is installing a new campus-wide 5G cellular network. This technology will be used for future project work as well as to develop institute-wide expertise by performing hands-on testing on 5G cellular networks. This project was initiated to perform a penetration test on the 5G network with the intent of expanding SwRI’s previous 4G LTE testing experience and update it into the 5G sphere, while simultaneously performing a security assessment of the 5G network and associated technologies used on SwRI campus.

Figure 1: Test Setup.
Approach
The penetration test was initiated by assuming that the 5G core would be physically inaccessible, therefore all testing would be performed either wirelessly or between the 5G core and the base station. Cellular testing included the following attack vectors:
- SIM card tampering and spoofing
- Interception of hardline communication between base-station and core
- Cellular signal jamming and spoofing via software defined radios
- Cellular device fuzz testing
Accomplishments
The project yielded in vulnerability discoveries of the campus 5G system, allowing for development of mitigation strategies. Techniques generated during the project allowed intercepting and modifications of transmitted user data over 5G networks.

Figure 2: Legitimate SIM & Cloned Programmed SIM.
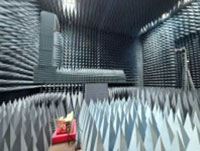
Figure 3: gNodeB – Legitimate 5G Signal.

Figure 4: SDRs – Jamming and Spoofing.
